Hackers are moving away from attacking hardened operating systems, applications, and networks and zeroing in on tech’s most vulnerable and foundational element: firmware. Every computing device has firmware, and the technology that powers autonomous vehicles (AV) and electric vehicles (EV) is no exception.
In addition to the growing firmware threat, increased connectivity among all AV and EV systems, including charging stations, creates a significantly expanded attack surface area. An automotive firmware infiltration can give hackers the highest level of access to a driving system’s critical components, allowing them to inflict severe damage—from overriding safety protocols to taking complete control.
Phoenix collaborates closely with leading Tier 1 autonomous vehicle and electric vehicle system providers, like Baidu/Apollo, to architect complete autonomous vehicle firmware solutions.
Our software is built to support electric vehicle systems and the L4/L5 future of autonomy based on our deep understanding of the critical roles that firmware and firmware security play in the modern automotive industry.
As the original independent firmware company, Phoenix has over 40 years of experience developing, deploying, and patching firmware across various devices. We work closely with leading silicon vendors Intel, AMD, Qualcomm, Arm, and NVIDIA. We also maintain deep-rooted relationships with major organizations that support firmware security like the Unified Extensible Firmware Interface (UEFI) Forum and DMTF (formerly the Distributed Management Task Force). Our core firmware development team is based in Silicon Valley with engineering teams around the world, including in the US and Taiwan.
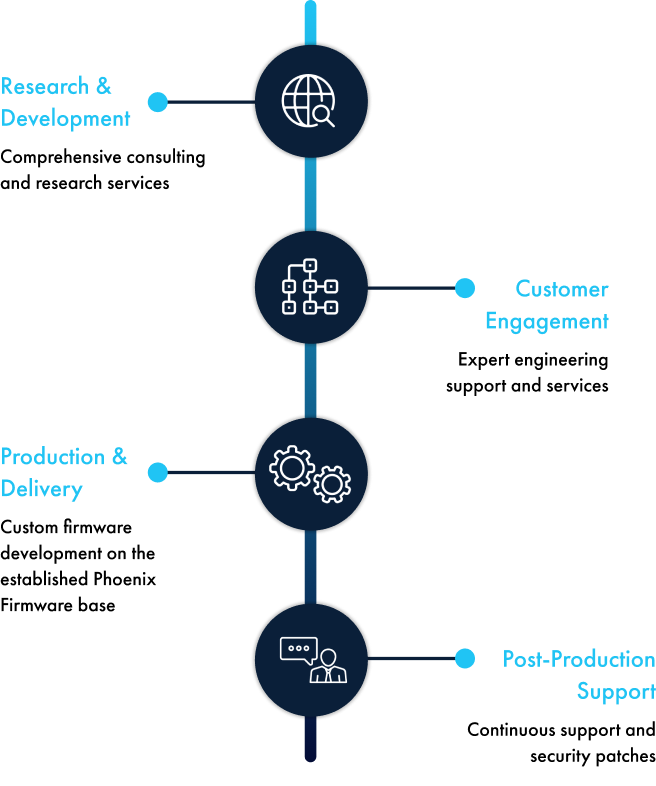
At Phoenix, we partner with you throughout the entire firmware life cycle, from the initial development and deployment through post-production and ongoing security patches release.

Take advantage of our security-as-a-service for an added layer of post-production support.
Autonomous vehicle OEMs can also take advantage of our firmware security-as-a-service program. This annual support package includes the monitoring and notification of identified firmware vulnerabilities. Partners who leverage Phoenix FirmCare can also take advantage of rapid patch creation and delivery to ensure that firmware and the vehicles running on it stay protected. The program includes:

Our team monitors the universe of firmware threats, tapping into black hat and DEF CON resources and other industry research entities.

You can expect to receive reports on firmware threats weekly, monthly, or annually, depending on service level agreement (SLA), with suggested fixes for every identified vulnerability.

The Phoenix Security Team will mimic a hack on a target machine to uncover weak spots in existing firmware, then suggest solutions.

Our test lab can conduct penetration testing (pen testing) both internally and at federal laboratories to locate any system vulnerabilities and advise on improvements.
Company
Partners
Market Segments
Firmware Expertise
Products + Solutions
Services + Support
Legal
Copyright © 2025 Phoenix Technologies Inc. All rights reserved | Privacy Policy | Terms of Use | Cookie Policy | Trademarks
For any matters related to the domain phoenix.com, please contact [email protected]