I am guessing most people didn’t pay much attention to the official release of the Common Vulnerability Scoring System (CVSS) 4.0 this month. This may sound like a “non-event”, but if you are trying to make the world aware of the severity of a software vulnerability it is a strong step forward.
CVSS is an open standard that is used by security professionals everywhere. In fact, Phoenix uses it each time we issue a final pen testing report to our customers. We are currently using version 3.1 but will be migrating to version 4.0 in the coming months.
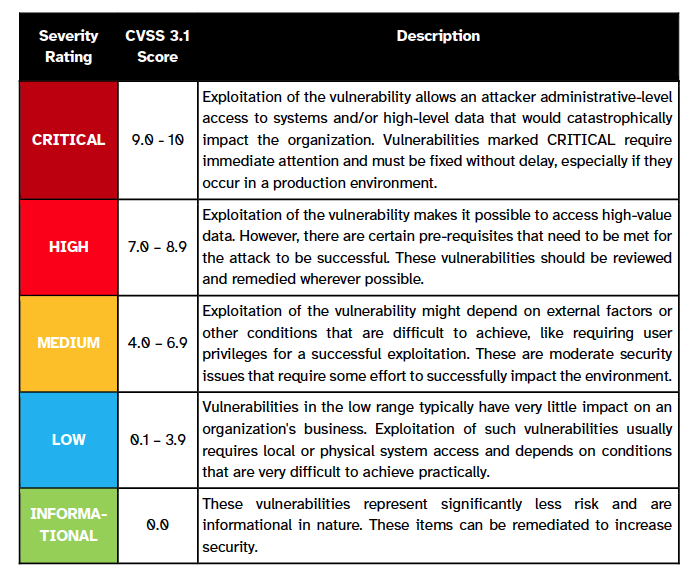
The CVSS scoring system was launched in February 2005 with the ambition to become the de facto open source, scoring system for severity ratings of software vulnerabilities. It has reached that goal with widespread adoption. The custodian for CVSS is the Forum of Incident Response and Security Teams (FIRST). First describes the improvements in version 4.0 as follows:
“The revised standard offers finer granularity in base metrics for consumers, removes downstream scoring ambiguity, simplifies threat metrics, and enhances the effectiveness of assessing environment-specific security requirements as well as compensating controls. In addition, several supplemental metrics for vulnerability assessment have been added including Automatable (wormable), Recovery (resilience), Value Density, Vulnerability Response Effort and Provider Urgency. A key enhancement to CVSS v4.0 is also the additional applicability to OT/ICS/IoT, with Safety metrics and values added to both the Supplemental and Environmental metric groups.”
More details can be found in the FIRST press release for CVSS 4.0.
Author
-

Ameet is responsible for global marketing and business development. He has worked with a wide variety of companies from large multinationals such as IBM and Fujitsu to startups like Swan Labs (acquired by F5 Networks) and Shenick Networks (acquired by Aeroflex). Ameet has a Bachelor of Science in Electrical Engineering from North Carolina State University and an MBA in Marketing from the Wharton School at the University of Pennsylvania.
View all posts